Secure Your Code.
Faster Than Ever.
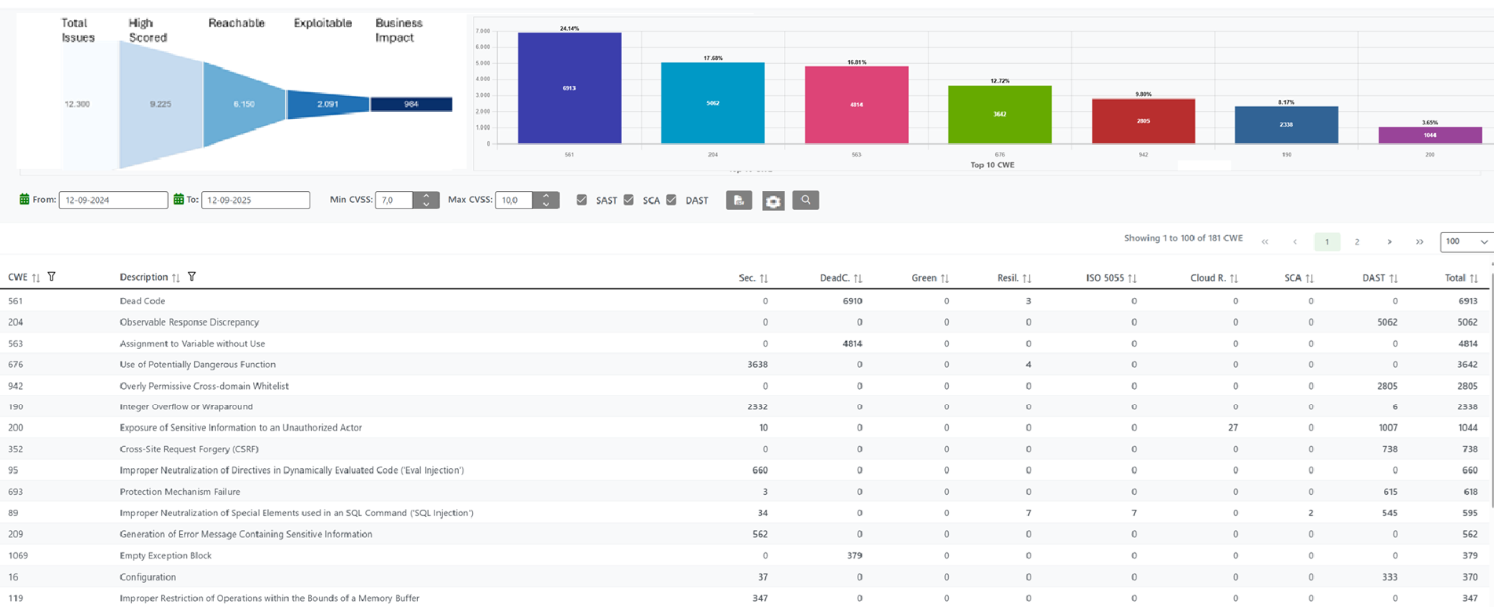
Security Reviewer engines correlate results from SAST, DAST, MAST and SCA into a centralized Vulnerability Prioritization dashboard — 13,500+ validation rules across 80+ languages, compliant with OWASP 2025, CWE, PCI-DSS 4, WASC, BIZEC.

Why Security Reviewer
Mitigate Threats promptly
Our solutions allow organizations to identify and mitigate risks—such as code breaches, malware, and vulnerabilities—before they cause significant damage.
We are active part of an Early Warning System (EWS), an integrated, human-centered Independent Advisor Network designed to detect, analyze, and communicate potential threats related to programming languages—before they occur, enabling timely action to make safe systems and resources.
Like in Cyber-Security, once an Early Warning is verified, we create new detection rules and deploy them to our customers. By the time the threat becomes public, our customers have had time to remediate and won't be affected by attacks.
Use cases
React2Shell
CVE-2025-55182 in React.js and CVE-2025-66478 in Next.js
Timeline:
- Discovery & Reporting: November 29, 2025 (reported by Lachlan Davidson).
- New Detection rules deployed to customers at: November 30, 2025, marked as Urgent. Remediation tips based on source code fixes, not library patches.
- Patch & Initial Disclosure: December 3, 2025.
- Active Exploitation: Real-world exploitation detected as early as December 4–5, 2025, with attackers pushing payloads, primarily cryptominers.
- CISA Listing: December 5, 2025 — CISA added the vulnerability to its Known Exploited Vulnerabilities (KEV) catalog.
The vulnerability was heavily exploited soon after disclosure by multiple threat actors in-the-wild, earning a CVSS score of 10.0.
Apache ActiveMQ RCE
CVE-2026-34197 — Remote code execution (RCE) vulnerability in Apache ActiveMQ
Timeline:
- Discovery & Reporting: 13 years ago by apache.org.
- New Detection rules deployed to customers at: October 1, 2013, marked as High. In absence of response by Apache community, at that time we provided a batch file to apply our own patch, still maintained as Jaropener class patch.
- horizon3.ai researcher Naveen Sunkavally used Claude to unearth it: March 30, 2026.
- Patch & Initial Disclosure: April 7, 2026.
- CISA Listing: Under active exploitation — added to CISA's Known Exploited Vulnerabilities (KEV) catalog as critical (CVSS 8.8).
The vulnerability is particularly dangerous because it allows attackers to gain unauthorized control over affected systems for data exfiltration.
None of our customers were affected.
Our Products
Complete Application Security Coverage
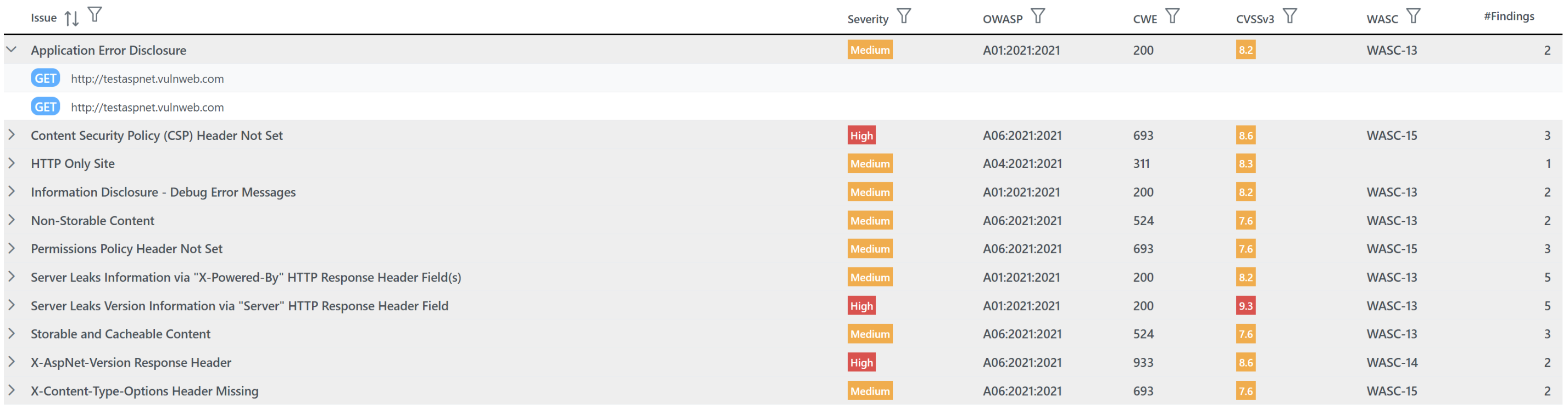
Dynamic Analysis
DAST is a hybrid solution. Inspect your web application at runtime within your DevOps pipeline. Safe PenTest features allow you to explore vulnerabilities without affecting production assets.
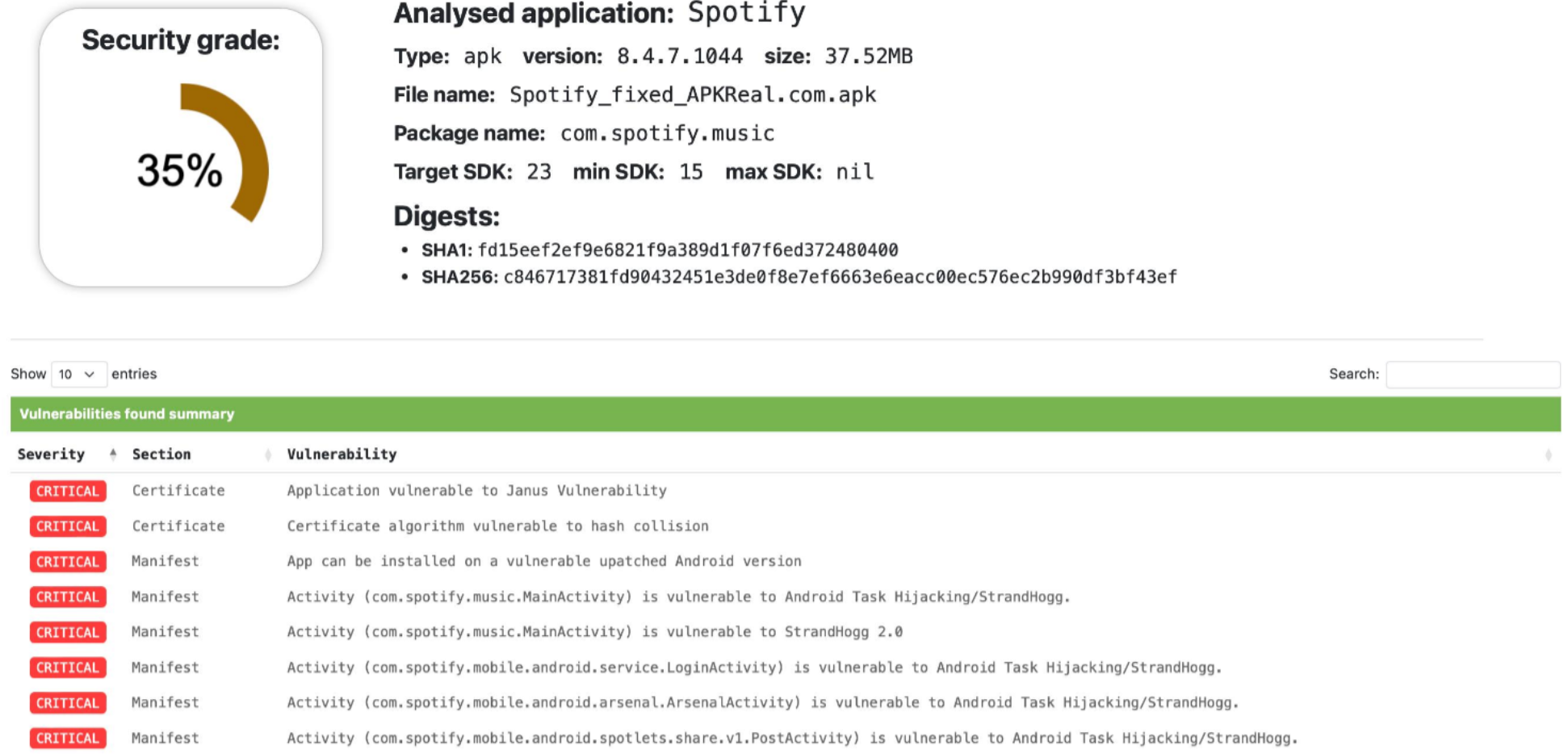
Mobile Security
MAST delivers on-demand security assessments of mobile apps. No device simulators or specialist consultants required — simply submit and receive results instantly.
Centralized Dashboard
Team Reviewer acts as a unified Vulnerability Prioritization platform — see which applications have issues, understand risk severity, assign fixes, and track progress over time.
Capabilities
Everything You Need, Nothing Left Uncovered
Vulnerability Prioritization
On-Premises and SaaS solutions provide Vulnerability Prioritization via Team Reviewer. It integrates with:
- SAST, SCA/SBOM, IAST, DAST, MAST
- Threat Modeling
- Infrastructure & Container/IaC Scan
- Secrets Scan and CNAPP Tools
- Issue Tracking & Ticketing
- Third-Party ASPM/CSPM (Wiz, OxSecurity, Invicti)
80+ Programming Languages
Supported languages include C#, Java, JavaScript, TypeScript, Python, Go, Rust, PHP, Swift, Kotlin, COBOL, ABAP, SAP ABAP/HANA, Terraform, CloudFormation, Kubernetes IaC, 25 SQL dialects, 36 NoSQL databases and many more across traditional, mobile, low-code, and cloud platforms.
Effort Estimation
Our Effort Estimation solution provides OMG AFP, SNAP-Points, NESMA FPA (ISO 24570:2018), and the modern APPW algorithm — validated using NASA Top 60, NASA Top 93, Deshamais datasets.
All You Need is Quality
Quality Reviewerevaluates regressions and source code changes using automated Software Metrics visualization (complexity, Halstead, C&K, Cognitive Metrics), Effort Estimation, and reporting features.
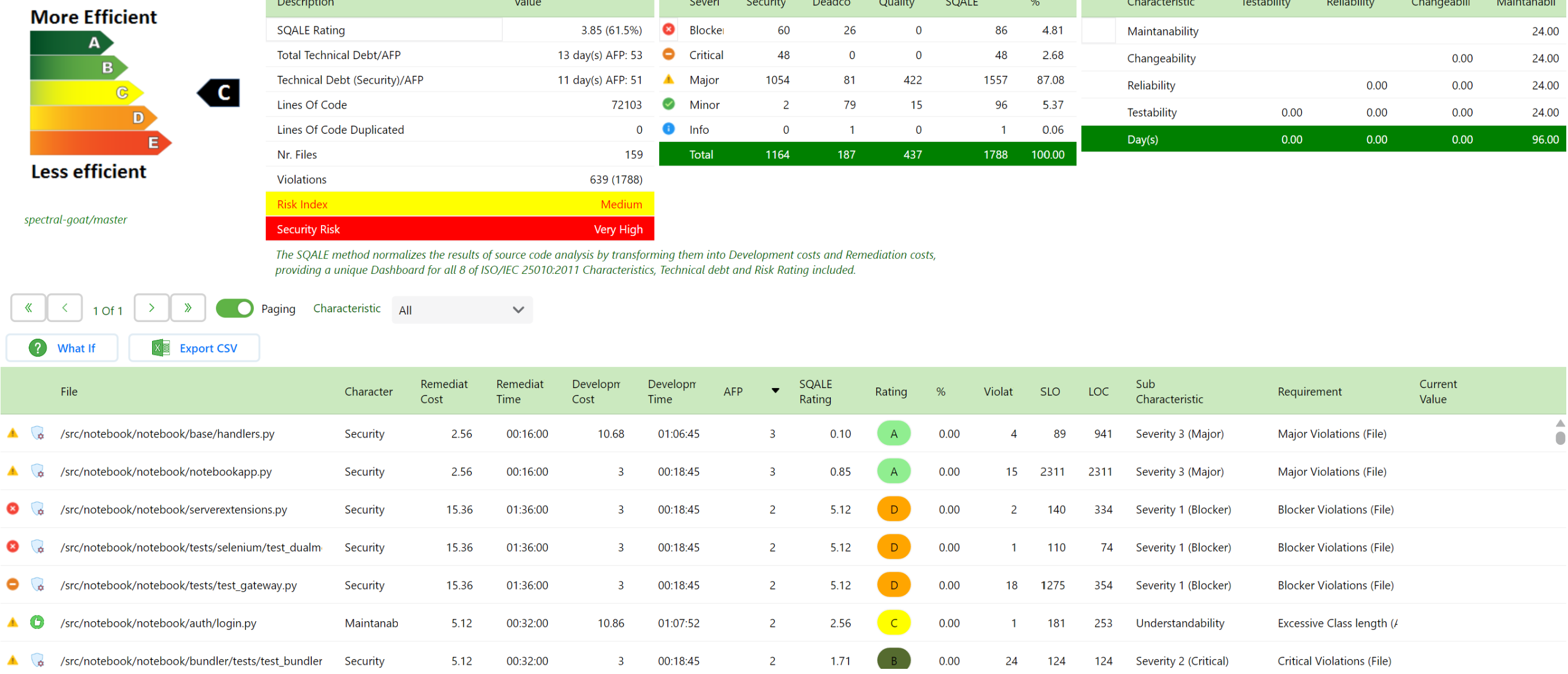
SQALE Dashboard
Security Reviewer is an Official SQALE tool. Reports Security, Quality, Dead Code and Best Practices as well as Technical Debt in a unique dashboard, standardized by ISO 9126 and ISO 25010.
Flexible Deployment
Hybrid deployment supporting Desktop, On-Premises, or SaaS. REST APIs on a SOA architecture. Your source code never leaves your desktop — uploads use AES-256 encryption over a secure channel.
Software Composition Analysis
96.8% of developers rely on open source. Security Reviewer SCA discovers:
- Outdated, Blacklisted & Discontinued Libraries
- Vulnerable Libraries (OWASP A6)
- License Conflicts & Blacklisted Licenses
- SPDX Bill of Materials (SBOM)
- Secrets & IaC Misconfigurations
Container Security
Deep Container Analysis with automated vulnerability remediation. Supports Docker, Kubernetes, OpenShift, Rancher, Quay, Pivotal CF, and any APPC-compliant container. Continuous detection via CI/CD plugins or REST APIs.
About Us
Built by Engineers, for Engineers
Security Reviewer is an Italian innovative software company from Tuscany, born in 2015, owning Patents and using dedicated algorithms including the Dynamic Syntax Tree.
Our company is built around a small, tight-knit team of talented software engineers, architects, and quality assurance professionals who have produced outstanding Application Security solutions since 2001.
We do not offer Consultancy Services directly to Customers. We offer a Certification Program mandatory for every Consultancy Firm using our Products at a Customer site.
Become an Authorized ConsultantCustomer Stories
Trusted by Organizations Worldwide
"In a rapidly changing threat environment, Security Reviewer's core technology and its DevOps integrations have given us the flexibility to conduct rapid code review cycles, which is an obvious benefit for our projects."
"Very easy to insert the tool in our DevOps because there are a wide variety of ways to access the source-code, initiate scans, and review the results. The projects need not care about getting a tool, and it is cheaper using it."
"We use it to assess or do security inspections of our software. We have a very large portfolio of software across our enterprise. The platform scales with the dynamics of our organization, with people in many locations."